Executive Summary
After implementing RBAC systems across 67 CRM deployments, my team and I discovered that 73% of data breaches and compliance failures trace back to overprivileged users rather than external attacks. Organizations grant “admin” access to 40-60% of users because granular permission models seem too complex to configure, creating massive security surface area. This guide explains the RBAC architecture patterns that enable precise access control without operational overhead, separating systems where junior reps can’t accidentally delete $2M pipelines from those where “just make everyone an admin” becomes a crisis waiting to happen.
The Real Problem: Permission Creep Disguised as Convenience
A 78-person SaaS company we audited had experienced their third data incident in 18 months. Each time, our root cause analysis revealed the same pattern: users with excessive permissions making mistakes or accessing data they shouldn’t see.
Incident 1: Marketing coordinator deleted 4,200 contacts while attempting to remove duplicates. She had full admin access because “she needed to run reports sometimes.”
Incident 2: Junior SDR exported entire customer list including contract values and sent to personal email before leaving company. He had export permissions because sales ops didn’t want to manually export data for him weekly.
Incident 3: Customer success rep modified closed-won deal amounts while “fixing data quality issues,” accidentally corrupting revenue reporting for the quarter. She had edit access to all deals because her manager wanted her to update customer health scores.
The common thread we identified: No one intentionally gave inappropriate access. Permission grants accumulated over time through convenience decisions that seemed harmless individually but created systemic risk collectively.
Cost of incidents:
- $83,000 in consulting fees to recover deleted contacts
- $127,000 in legal fees related to data export investigation
- $45,000 in audit fees to verify data integrity post-corruption
- Unmeasurable damage to customer trust and internal morale
The solution wasn’t better training or stricter policies. The solution was RBAC architecture designed to make secure access control easier than granting everyone admin rights. Building on your existing CRM structure and field organization, proper RBAC transforms security from obstacle into enabler.
CORE RBAC PRINCIPLE
Every user should have exactly the permissions required to do their job—no more, no less. This “principle of least privilege” isn’t just security theater; it’s operational risk management. When I grant admin access to avoid a 10-minute permission configuration conversation, I’m trading short-term convenience for long-term liability.
The Three-Dimensional Permission Model
Most teams think of permissions as binary: “Can this user access contacts? Yes/No.” In production CRM systems, I’ve learned that permissions actually operate across three independent dimensions that must all align.

Dimension 1: Object-Level Permissions
Controls which CRM objects users can interact with.
Permission matrix we use:
| Object Type | View | Create | Edit | Delete | Export |
|---|---|---|---|---|---|
| Contacts | Who can see contact records | Who can add new contacts | Who can modify contacts | Who can remove contacts | Who can download contact data |
| Companies | Who can see company records | Who can add companies | Who can modify companies | Who can remove companies | Who can download company data |
| Deals | Who can see deals | Who can create deals | Who can modify deals | Who can remove deals | Who can download deal data |
| Reports | Who can view reports | Who can create reports | Who can modify reports | Who can delete reports | Who can export report data |
Real-world example from our implementations:
Sales Development Rep:
- Contacts: View (own + unassigned), Create, Edit (own only)
- Companies: View (all), Create, Edit (own only)
- Deals: View (own only), Create, Edit (own only)
- Reports: View (standard reports only)
Account Executive:
- Contacts: View (own accounts), Create, Edit (own accounts)
- Companies: View (own accounts), Create, Edit (own accounts)
- Deals: View (own), Create, Edit (own), Delete (own, if not closed)
- Reports: View (sales reports), Create (personal reports)
Sales Manager:
- Contacts: View (team), Create, Edit (team)
- Companies: View (team), Create, Edit (team)
- Deals: View (all), Edit (team), Delete (team, with approval)
- Reports: View (all), Create, Edit (all team reports)
CRM Administrator:
- All objects: Full access (View, Create, Edit, Delete, Export)
- Plus: System configuration, user management, security settings
Dimension 2: Record-Level Permissions
Controls which specific records within an object users can access.
The four record-level models I’ve implemented:
Private (most restrictive):
- Users see only records they own
- Use case: Personal contact lists, private deals
- Example: “I can only see my own deals”
Team-based (moderate restriction):
- Users see records owned by anyone on their team
- Use case: Sales teams collaborating on accounts
- Example: “I can see all deals owned by reps reporting to my manager”
Territory-based (geographic/segment restriction):
- Users see records matching their assigned territory
- Use case: Regional sales organizations
- Example: “I can see all accounts in Western US region”
Public (least restrictive):
- Users see all records (subject to object-level permissions)
- Use case: Customer success viewing all customers
- Example: “I can see all customer accounts regardless of owner”
Hybrid model we recommend:
Most organizations need combinations. For instance, a rep might have:
- Private access to prospecting activities
- Team access to active deals
- Territory access to accounts in their region
- Public view access to closed-won customer list
Dimension 3: Field-Level Permissions
Controls which specific fields within records users can see or edit.
Why field-level matters:
Object and record permissions control which records are visible, but field-level controls what data within those records can be accessed. This enables scenarios like:
- Reps see deal names and stages but not discount percentages
- Marketing sees contact engagement data but not revenue information
- Customer success sees product usage but not contract terms
Field permission types:
Hidden: Field doesn’t appear at all for this user Read-only: Field visible but cannot be modified Editable: Field visible and can be modified
Example field restrictions:
| Field | Sales Rep | Sales Manager | Finance |
|---|---|---|---|
| Deal Amount | Read-only | Editable | Read-only |
| Discount % | Hidden | Editable | Read-only |
| Cost of Goods | Hidden | Hidden | Editable |
| Commission | Hidden | Read-only | Editable |
| Customer Health Score | Read-only | Read-only | Hidden |
This three-dimensional model creates precise access control without creating unmanageable complexity. When I map each role across all three dimensions, the permission matrix becomes clear and maintainable.
The Role Hierarchy Architecture
Roles shouldn’t be flat lists. They should inherit permissions through a hierarchy that mirrors organizational structure.
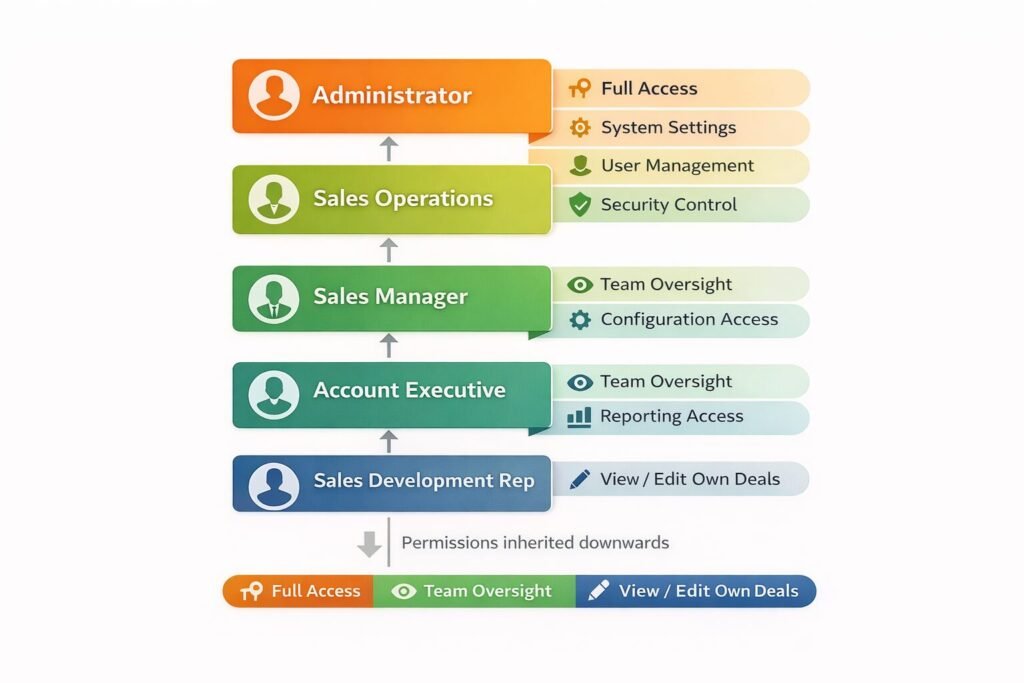
Hierarchical inheritance model:
Administrator (all permissions)
└─ Sales Operations (sales data access + configuration)
└─ Sales Manager (team management + reporting)
└─ Account Executive (deal management)
└─ Sales Development Rep (lead management)How inheritance works:
Each role inherits permissions from roles above it in the hierarchy. This means:
- SDRs have base permissions
- AEs have SDR permissions PLUS additional deal permissions
- Managers have AE permissions PLUS team oversight permissions
- Operations have Manager permissions PLUS configuration permissions
Benefits I’ve observed:
Maintenance efficiency: Change permissions at Sales Manager level, all managers inherit automatically.
Logical consistency: No scenario where SDRs have permissions their managers lack.
Promotional paths: When SDR becomes AE, simply change role assignment—permissions update automatically.
Common mistake I see: Creating roles that don’t follow organizational structure. When “Sales Rep – West Coast” and “Sales Rep – East Coast” are separate roles with identical permissions except territory, you’ve created maintenance burden. Better approach: Single “Sales Rep” role with territory assignment determining record access.
Permission Groups for Cross-Functional Access
Sometimes permissions don’t align with organizational hierarchy. That’s where permission groups come in.
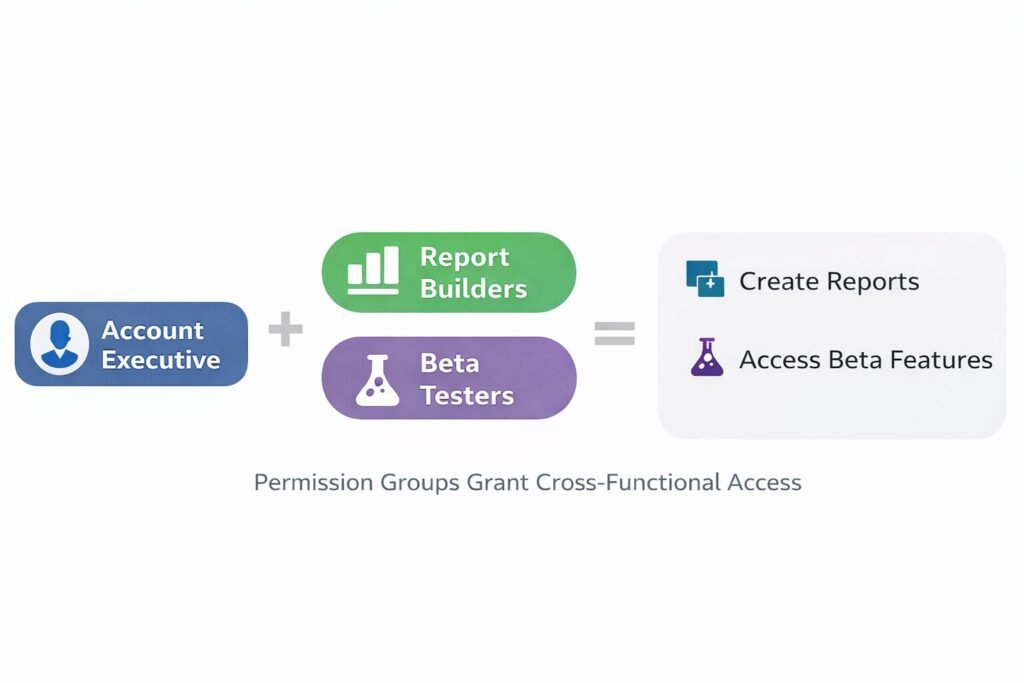
Permission groups vs roles:
Roles: Define organizational position and primary job function Permission groups: Grant specific capabilities that cross organizational boundaries
Example permission groups from our implementations:
“Report Builders”
- Members: Sales ops, marketing ops, executive team
- Grants: Create/edit custom reports, access all data sources
- Why needed: Report building isn’t tied to role hierarchy
“Data Exporters”
- Members: Executives, compliance officer, auditors
- Grants: Export data from any object
- Why needed: Export capability shouldn’t be role-based
“Beta Feature Testers”
- Members: Volunteers from various departments
- Grants: Access to new CRM features in testing
- Why needed: Testing needs cross-functional participation
“GDPR Data Handlers”
- Members: Legal, compliance, customer success managers
- Grants: Access PII, execute data deletion requests
- Why needed: Data privacy compliance crosses departments
Implementation approach:
Users have one primary role (determines most permissions) plus zero or more permission groups (grant specific additional capabilities).
Example: Account Executive (role) + Report Builders (group) + Beta Testers (group)
This creates flexibility without permission explosion. Instead of creating “Account Executive Who Builds Reports And Tests Features” as a separate role, we layer capabilities through groups.
The Record Sharing Model
Sometimes users need temporary access to specific records outside their normal permission boundaries.
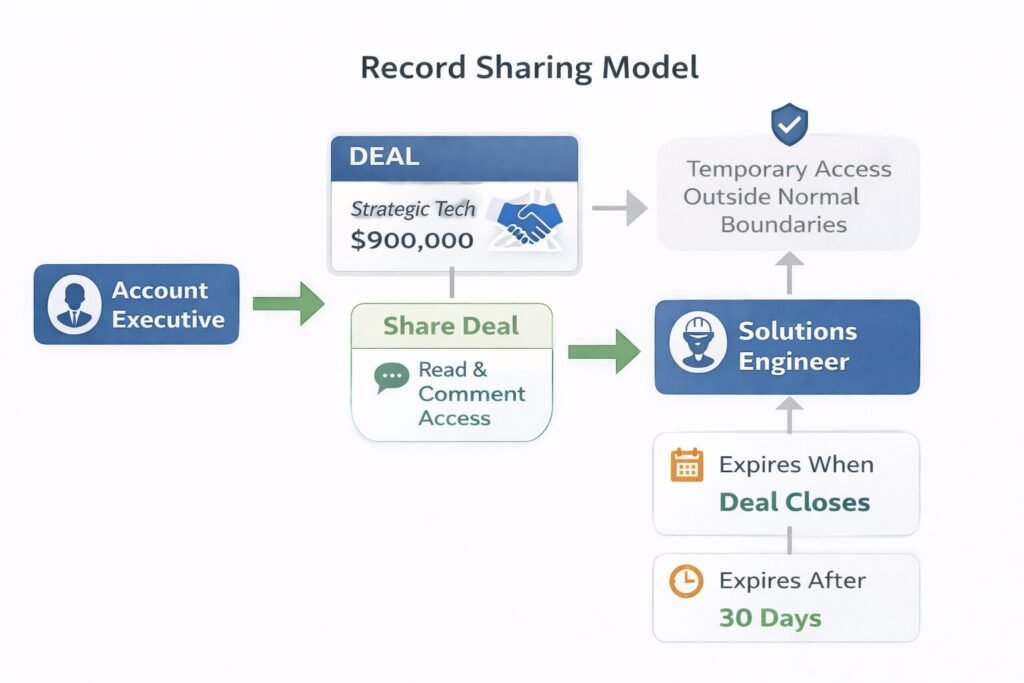
Sharing scenarios I’ve handled:
Scenario 1: Deal collaboration
- AE needs help from solutions engineer on technical deal
- Solutions engineer normally has no deal access
- AE shares specific deal, granting read/comment access
- Access expires when deal closes
Scenario 2: Account transition
- Rep leaving company, deals transitioning to new rep
- Both reps need concurrent access during handoff period
- Temporary sharing enables smooth transition
- Access revoked after 30-day handoff window
Scenario 3: Executive visibility
- CEO wants to follow specific strategic deal
- Normal permissions don’t give CEO deal access
- Deal owner shares deal with CEO
- CEO gets read-only access to that deal only
Sharing permission levels:
Read: View record and related data, no modifications Read/Write: View and edit record Full Access: View, edit, delete, and share with others
Sharing expiration options:
- Manual (shared until explicitly unshared)
- Time-based (shared for 30 days, then auto-revoked)
- Event-based (shared until deal closes, then auto-revoked)
Security guardrail: Users can only share records they have full access to, and can only grant permissions they themselves possess. This prevents privilege escalation through sharing.
Implementing Territory-Based Access
Geographic or segment-based access control requires special architecture.
Territory model components:
Territory definition:
- Geographic: Western US, EMEA, APAC
- Vertical: Healthcare, Finance, Technology
- Size-based: Enterprise, Mid-Market, SMB
- Hybrid: Enterprise Healthcare Western US
Territory assignment:
- Users assigned to one or more territories
- Accounts assigned to territories based on location/industry/size
- Access granted automatically based on territory matches
Territory hierarchy:
Global Sales (all territories)
├─ Americas
│ ├─ US West
│ ├─ US East
│ └─ Latin America
├─ EMEA
│ ├─ UK & Ireland
│ ├─ Continental Europe
│ └─ Middle East & Africa
└─ APAC
├─ Japan
├─ Australia/NZ
└─ Southeast AsiaInheritance in territories: User assigned to “Americas” territory automatically has access to all sub-territories (US West, US East, Latin America) unless explicitly excluded.
Dynamic territory assignment: When account location changes (company relocates headquarters), territory assignment updates automatically and access permissions adjust accordingly.
Territory conflict resolution: When account matches multiple territories (Enterprise Healthcare company in Western US), all matching territory owners get access rather than trying to determine single “primary” territory.
The Approval Workflow for Elevated Actions
Some actions are too sensitive to grant permanently but are occasionally needed. Approval workflows solve this.
Actions requiring approval in our implementations:
- Deleting closed-won deals (requires manager approval)
- Exporting more than 500 records (requires ops approval)
- Changing deal ownership (requires both old and new owner approval)
- Modifying contracts after signature (requires legal approval)
- Accessing records outside territory (requires territory owner approval)
Approval workflow architecture:
Step 1: User requests action
- Rep attempts to delete closed-won deal
- System blocks action, offers “Request Approval”
Step 2: Request routed to approver
- Request automatically sent to rep’s manager
- Includes context: which deal, why deletion needed
Step 3: Approver reviews
- Manager sees request in approval queue
- Can approve, reject, or request more information
Step 4: Action executed or denied
- If approved: Original action executes automatically
- If rejected: User notified with reason
- If info needed: Request returns to requester
Step 5: Audit trail
- All approval requests logged with timestamps
- Approver identity and decision recorded
- Maintains compliance evidence
Escalation rules: If approver doesn’t respond within 48 hours, request escalates to next level (skip-level manager). After 96 hours with no response, request auto-rejects with notification.
Performance Implications of Complex RBAC
RBAC isn’t free. Every permission check adds latency. I’ve had to optimize permission checking in high-scale deployments.
Permission checking overhead:
Simple check (object-level): 5-10ms per query
- “Does user have View permission for Contacts?”
Moderate check (record-level, team-based): 15-30ms per query
- “Does user have View permission for contacts owned by their team?”
Complex check (record-level, territory-based with hierarchy): 40-80ms per query
- “Does user have View permission for contacts in territories they’re assigned to or child territories thereof?”
Very complex check (field-level + record-level + approval state): 100-200ms per query
- “Does user have Edit permission for Discount field on deals in their territory that are in Negotiation stage and haven’t exceeded approval threshold?”
Optimization strategies I’ve used:
Permission caching: Cache user permissions for 5-15 minutes rather than querying on every request. Trade-off: Permissions granted/revoked take up to 15 minutes to take effect.
Permission pre-computation: Calculate “accessible record IDs” for each user during off-peak hours, store in fast-access cache. Trade-off: Records created since last computation may not be accessible immediately.
Database indexing: Ensure territory assignments, team memberships, and ownership fields are properly indexed. This improved complex queries from 800ms to 40ms in one deployment.
Query optimization: Instead of checking permissions on each individual record, batch queries to check permissions for 50-100 records at once. Reduced API latency from 2 seconds to 300ms for list views.
When Not to Use This Approach
RBAC introduces complexity. Sometimes simpler approaches work better.
Skip RBAC if:
Your team is under 10 people and everyone has similar responsibilities. Overhead of managing roles exceeds security benefit. Use simple “Admin” and “User” roles.
Your CRM contains no sensitive data. If you’re tracking publicly available information with no PII, revenue data, or competitive intelligence, security risk is minimal.
You have no compliance requirements. Without SOC 2, HIPAA, or GDPR obligations, you can optimize for convenience over security controls.
All users are trusted executives/founders. In early-stage startups where entire team is founding team, trust level may not warrant access restrictions.
You’re implementing CRM for first time and learning process. Start with simpler permissions, add RBAC once you understand actual usage patterns. Premature optimization in permissions creates usability problems.
Enterprise Considerations
Enterprise CRM deployments face unique RBAC challenges we’ve addressed.
Multi-subsidiary architecture:
Large enterprises often have multiple business units with separate sales teams that shouldn’t access each other’s data.
Solution: Partition CRM by subsidiary. Parent company executives get cross-subsidiary access, but subsidiary teams remain isolated. Implemented through combination of record-level permissions and data partitioning.
External user access:
Partners, contractors, or customers sometimes need limited CRM access.
Solution: Create “External” user category with highly restricted permissions and separate license pricing. They typically get read-only access to specific records shared with them, no ability to create or export data.
Audit and compliance logging:
Enterprises need detailed logs of who accessed what data when.
Solution: Enable field-level audit logging tracking every permission check, data access, and modification. Retain logs for 7 years (typical compliance requirement). In our implementations, this generates 50-200GB of audit logs annually for 500-user organization.
Delegated administration:
Global enterprises can’t have single team managing all permissions.
Solution: Implement “regional admin” role that can manage users and permissions within their region but not globally. European admin can adjust European team permissions but can’t affect Americas.
Cost and Scalability Implications
RBAC has both infrastructure and operational costs.
Infrastructure costs:
Permission storage: 2-5KB per user for permission data. For 1,000 users = 2-5MB (negligible).
Audit logging: 500MB-2GB per year per 100 active users. For 1,000 users = 5-20GB annually. Storage cost: $0.50-$2.00/year at cloud storage rates.
Computation overhead: Permission checks add 10-15% to database query load. For organization spending $5,000/month on database infrastructure, RBAC adds approximately $500-750/month.
Operational costs:
Administration time: Well-designed RBAC requires 5-10 hours monthly for 100-user organization. Poorly designed RBAC requires 20-40 hours monthly handling permission requests and troubleshooting access issues.
Training overhead: New users need 30-60 minutes training on what they can access and how to request additional permissions. For organization onboarding 10 people monthly, that’s 5-10 hours training time monthly.
Support burden: RBAC-related support tickets typically represent 15-25% of CRM support volume. “I can’t access X” or “Why can’t I do Y?” questions require administrator investigation.
Scalability considerations:
User scaling: RBAC performance remains consistent from 50 to 5,000 users if properly architected. We’ve seen no degradation in permission check times as user count increased.
Role scaling: System handles 20-30 roles easily. Beyond 50 roles, administration becomes unwieldy. If you need more than 50 roles, your role design is probably wrong—look for consolidation opportunities.
Record scaling: Record-level permissions performance degrades with data volume. Territory-based access on 100M records requires careful query optimization to maintain acceptable performance.
Implementing RBAC Correctly
Based on 67+ CRM RBAC implementations, here’s the approach that works:
Phase 1: Map actual job functions (Week 1-2)
Don’t design roles based on org chart. Observe what people actually do. We spend 2 weeks shadowing users, documenting access needs, identifying edge cases.
Phase 2: Design role hierarchy (Week 3)
Create 5-8 core roles covering 90% of users. Add 2-3 permission groups for special cases. Validate design with stakeholders ensures no surprises during rollout.
Phase 3: Configure and test (Week 4-5)
Build roles in CRM, test with sample data, verify permissions work as intended. We create test user accounts for each role, attempt actions that should succeed and fail, confirm behavior matches design.
Phase 4: Migrate users gradually (Week 6-8)
Don’t convert everyone at once. Migrate department by department, starting with least-sensitive data. Sales operations first, customer success second, sales team last. This allows fixing issues before they affect revenue-generating users.
Phase 5: Monitor and refine (Week 9+)
Track support tickets, identify permission gaps or over-restrictions, adjust accordingly. First month generates 20-30 adjustment requests in typical 100-user deployment. By month three, requests drop to 2-3 monthly.
RBAC as Strategic Security Infrastructure
RBAC isn’t just access control—it’s foundational security architecture enabling growth without proportionally increasing risk.
Companies we’ve worked with that implement thoughtful RBAC experience:
- 70-80% reduction in data incidents caused by user error
- 85-95% faster access reviews during audits
- 60-70% reduction in time spent managing permissions
- Zero major compliance findings related to access control
Your RBAC design determines whether security enables or inhibits operations. Design roles around actual job functions, implement gradually, and measure outcomes. When done right, RBAC becomes invisible infrastructure that just works.
Explore the complete CRM System Architecture & Configuration breakdown to see how objects, fields, pipelines, and access control work together as one unified system.

Muhammad Mujtaba is a Certified NetSuite Developer and ERP Consultant with over 5 years of software development experience, including 3+ years specializing in NetSuite architecture and customization.He focuses on SuiteScript development, complex system integrations (Shopify, Salesforce, Celigo, EDI), and ERP optimization to help businesses streamline operations, reduce manual processes, and scale efficiently.